
Features
Automating visitor management
June 27, 2022 By Ian Holmes
 monkeybusinessimages / iStock / Getty Images Plus
monkeybusinessimages / iStock / Getty Images Plus How can organizations create safe working environments that people actually want to visit?
For many, visitor management systems are the answer. Visitor management systems are becoming ever more commonplace as part of facility management strategies for government buildings, workplaces, schools and medical facilities. When combined with self-service technology, these systems become an important first step in a visitor’s journey, offering a pleasant and frictionless experience for customers, contractors and employees.
Safety first: the problem of human error
Yesterday’s reception areas ran entirely on human power. A visitor would enter the building and head to security or a welcome desk, where they told the attendant or receptionist the purpose of their visit while providing identification. That attendant would then verify the visitor with the building occupant and type the visitor’s information into the system to create a visitor pass.
Unfortunately, humans are prone to error. Information can be keyed incorrectly, the building employee could be hard to find, and the visit may be unexpected. With the possibility of dozens of visitors arriving at once, each needing access to different areas to connect with different people, a receptionist or security attendant could become overwhelmed.
In addition, they’re not only expected to be on top of the visitor schedules, but also be able to spot fraudulent IDs from different states, provinces and countries. It’s easy to see how an individual could be granted access to the wrong area or allowed to enter somewhere that should be restricted to vetted employees and contractors.
Automating for a warm (and secure) welcome
On the other hand, an automated visitor system virtually eliminates user error, establishing a more secure building for visitors and staff alike. Sophisticated self-service systems allow visitors to register themselves at multiple kiosks rather than waiting for a security attendant. Modern self-service kiosks often feature a document reader that simply scans a credential verifying their visit and, depending on the level of security needed, scans their identification. Removing the task of manually entering information into a security system speeds up the registration process while leaving reception and security staff free to better cater to the needs of visitors and staff alike.
Understanding credentials
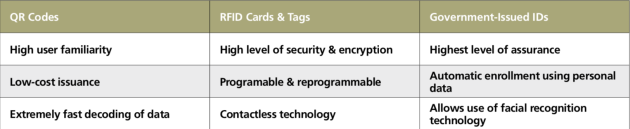
What we refer to as “credentials” are typically either a document, card or data token issued to an individual by a third party that grants them access to the premises while on site. These credentials can include a visitor badge, printed or digital QR code (2D barcode), a radio frequency identification card or government-issued IDs such as passports or driving licences.
Following a visitor’s registration, either online or at the point of entry, one or more of these credentials or tokens can be used by an individual while navigating the building. This includes a final check-out before leaving the site — a crucial last step for fire safety and contact tracing purposes. For more secure applications in data centres, schools or government buildings, government-issued IDs can also be used to enroll a visitor before providing them with access to secure areas on-premises. Let’s take a closer look at the common types of credentials that a visitor management system can process.
Understanding readers
Once a visitor has registered and has been issued a credential, that data token or ID document needs to be read by a device at a point of entry. These readers are usually positioned on a reception desk or fitted to an unattended self-service kiosk alongside other peripherals for printing badges or issuing access cards.
Readers are often connected via USB to a host PC with the visitor management or access control software running locally.
Embedded computing and Internet of Things (IoT) technology allow highly capable devices to communicate directly with a server or cloud service via a local area network for easy deployment and integration. IoT-ready devices are widely used today in airports and on public transport networks to improve passenger flow and experience.
The best visitor management systems are capable of accepting whichever credential an organization is currently using. For example, a building with multiple tenants may have multiple security systems.
In one company, the internal person attaches a QR code to the meeting invite; when the visitor arrives, they’ll scan that code at the kiosk. Meanwhile, another may simply request a visitor arrive, register on the enrolment kiosk and scan their driver’s licence or national ID card.
Security requirements can also be dependent on the type of visitor. After all, a person attending an interview poses a much lower threat to an organization than a contractor, so the credentials they are required to provide at entry should reflect this.
In this case, an organization may wish to issue the prospective employee a temporary barcode to be read from their phone or a printout when they arrive on site. However, as the contractor will have access to secure areas, it would be prudent to enroll them using their government-issued ID. Ideally, both the temporary barcode and government ID can be read and verified on the same device.
Accurately and efficiently capture data
Organizations can use multi-modal devices to read identity documents and automatically capture personal data, barcodes and high-resolution images of the presented ID.
An example is the HID ATOM ADR300 multi-illumination electronic machine-readable travel document reader. It employs optical character recognition technology to automatically read personal data such as the holder’s name, document number and address from the ID and output it to the visitor management system. This data can then be used to enroll a new visitor or cross-check against a list of pre-registered visitors or employees.
Images of an ID captured using multiple wavelengths of light (white, infrared and ultraviolet) to expose the printed visible and invisible security features can be used to complete automatic authentication.
A wide range of authentication techniques is used to determine whether the document is genuine or not, including the detection of optically variable inks, UV pattern matching, and cross-checking of personal data in the machine-readable zone, visual inspection zone and biometric chip.
For further assurance in self-service or partially attended applications, a facial image extracted from the document data page or biometric chip can be used to complete a 1-to-1 face match with a live image of the document holder to ensure the visitor is who they report to be.
This ability to read different national IDs, barcodes, RFID cards and even EU Digital COVID Certificates on a single device allows a visitor management system to accommodate a much wider range of visitors.
The future of visitor management starts now
The world is becoming ever more connected due to global trade and cultural exchange. As a result, organizations and workplaces are transforming from national to international entities at an unprecedented rate.
The systems used to manage the multitude of individuals attending a site need to be as flexible and dynamic as the organizations deploying them. The use of multi-modal devices provides a simple, single touchpoint for all types of visitors across an entire global organization for a safer — and simpler — world.
Ian Holmes is a business development manager for identity and security at Access IS, an HID Global company (www.hidglobal.com).
Print this page